At my employer, an IT business, we are quite aware of energy consumption. Now, I wanted to know how much energy my home office, and other home appliances, do use. Here’s some of the results. …
Continue reading
about what my curiosity has found

At my employer, an IT business, we are quite aware of energy consumption. Now, I wanted to know how much energy my home office, and other home appliances, do use. Here’s some of the results. …
Continue reading
I recently started the development of a vue3 application (web.replayer.app) and wanted to explore how to automatically build and deploy from my GitHub repository to my online test environment. Azure Pipelines seems to be an easy way to do it.
Continue reading
This should be a minimal guide to get you started with a VueJs PWA (Progressive Web App) from scratch. To learn more about PWA, you may listen to the PWA episode on the Coding Blocks …
Continue reading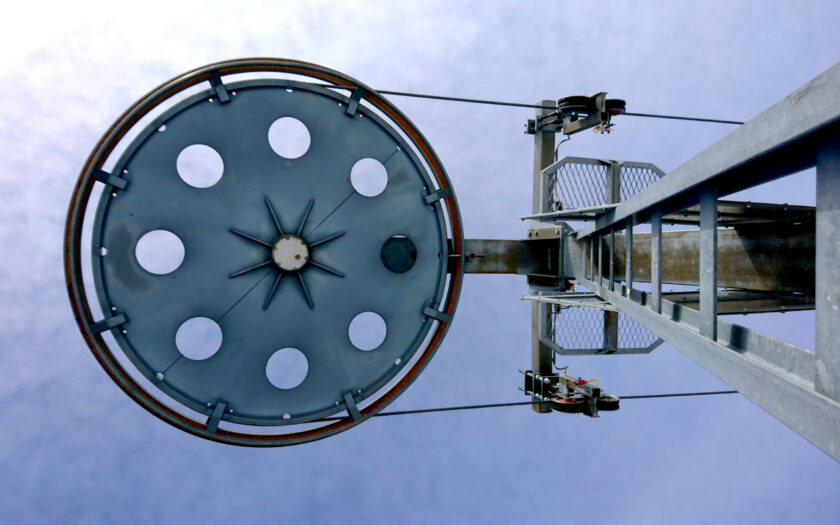
Over the years I have been using the Synology Moments app with all it’s AI goodness, but actually finding some of my photos remained difficult. Sometimes I remembered that a photo was taken with a …
Continue reading
Pi-hole is a popular DNS resolver, advertised as a black hole for Internet advertisements. I use it as a DNS filter for parental control as well as an ad and tracking domain filter. As a …
Continue reading
The other day, I wondered how to enable dark mode on any of those bright shiny websites. Before long, I found darkmode-js. Here’s how to use it with Tampermonkey.
Continue reading
I have scanned all my slides into TIFF images. Now, I want to improve the color curves a bit and convert them into shareable JPEG files. Marking the files As a first measure, I wanted …
Continue reading
Finally, I took the time for digitizing all those slides I had packed up in boxes and magazines some time ago. It’s more than 3200 slides and I wanted to avoid the costs of a …
Continue readingHow to use the exiftool on a Synology NAS
Continue reading
I tried to leverage the exiftool to help me manage my photo library, especially my received WhatsApp image files. These image files are quite heavily, lossy, compressed when sent and stripped of nearly all useful …
Continue reading